Progress of work
Progress of work
The client contacted us in a state of emergency. Their online presence (websites), which was critically important for engaging investors and end-buyers, was almost completely paralyzed.
Initial Picture:
- Complete Failure: Two of the four main corporate websites, which hosted current residential complexes and sales information, completely stopped working, displaying only errors or a blank page.
- Threat of Spread: All four resources were hosted on the same hosting provider, without proper isolation between accounts. This became the main reason for the mass infection.
- Infection Found: Express diagnostics showed that three of the four sites were infected with aggressive malicious code.
Diagnostics: Identifying the “Smart” Virus
The first stage involved a deep investigation into the nature of the virus and the extent of the damage. It turned out that we were dealing not with a simple defacement (content replacement) but with a tricky and well-masked piece of malware.
Virus Details and Actions:
- Malicious Code with Backdoor: The virus was a malicious script that created a hidden backdoor in the file system. This backdoor granted attackers constant and unrestricted access to all website files.
- Self-Recovery Mechanism: The biggest difficulty was the mechanism of spread and self-recovery. The virus generated its copy in almost every folder, across hundreds of files, masquerading as legitimate system files or plugins. If we deleted one copy, the remaining hidden copies would instantly restore it within seconds.
- Masking: The code was masked as a file supposedly being a “site security analyzer.” This was classic social engineering: a virus disguised as an antivirus.
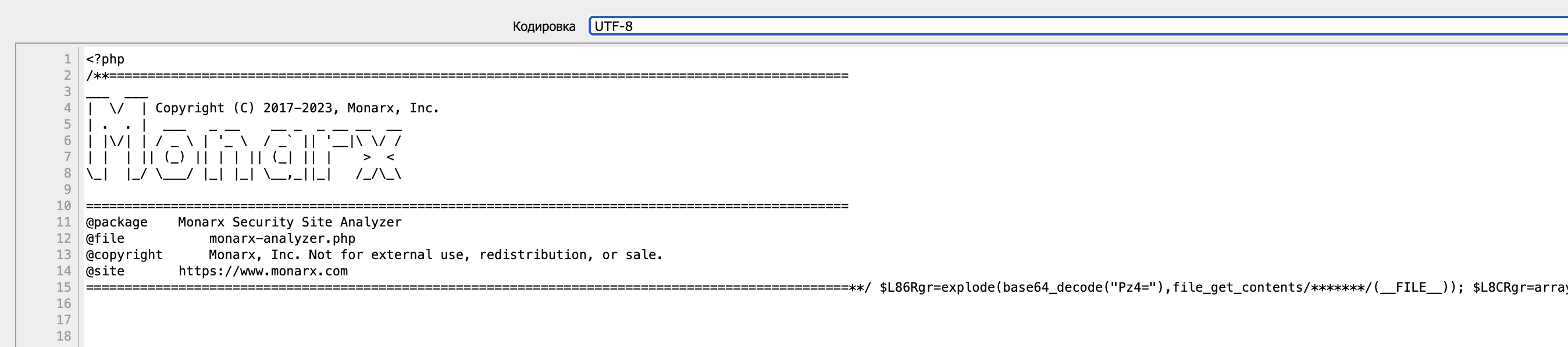
- Data Consequences: Due to the uncontrolled activity of the virus, which likely aimed to steal data or place phishing content, a significant portion of files from two websites was deleted. This led to their complete failure.
- The Main Challenge: Due to the complex directory structure (thousands of files on each site) and the immediate self-recovery of the virus, manual cleaning was impossible and entirely ineffective. A comprehensive strategy of isolation and automated disinfection was required.
Treatment Plan: Phased Strategy of “Isolation and Disinfection”
Our team developed a clear plan of five key stages to guarantee the complete removal of the virus and reliable restoration of functionality.
Stage 1: Emergency Backup and Search for Clean Copies
- Backup Requests: We immediately contacted the hosting support to obtain the latest backup copies.
- Backup Analysis: Unfortunately, most backups turned out to be infected, as the virus had been active for some time. However, we carefully sifted through the archives and managed to extract several critically important, undamaged files that helped restore the basic structure of the two “killed” websites.
Stage 2: Isolation and Threat Localization
- Full Download: To stop the virus’s self-recovery mechanism and its spread between sites, we completely downloaded all files of the three infected websites from the hosting to local secure servers.
- Work in Isolation: All subsequent work on cleaning and scanning was conducted in an isolated, offline environment where the malicious code could not execute or receive external commands.
Stage 3: Deep Cleaning and Disinfection
- Scanning with Specialized Tools: We used powerful antivirus scanners configured to identify hidden backdoors, encoded strings, and files with high entropy (characteristic of viruses).
- Manual Critical File Review: After the automated scan, our specialists manually checked the key system files to ensure that no hidden code remained.
- Replacing Core and Plugins: This was a critical step. We completely deleted the old CMS kernel (WordPress) and all installed plugins. New, clean versions, downloaded exclusively from official repositories, were installed in their place. This guaranteed that we would not accidentally reintroduce an infected plugin.
- Database Cleaning: Databases were also thoroughly checked for injections of malicious scripts into user, option, or post tables.
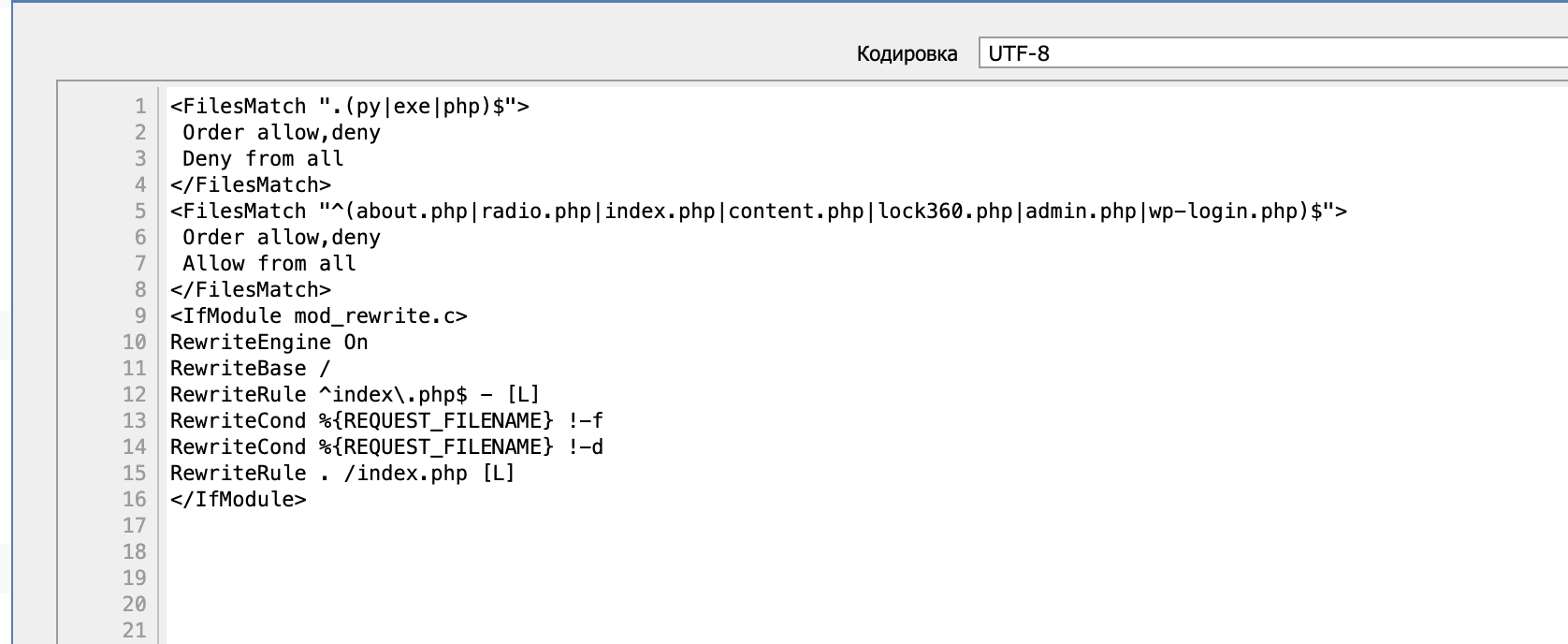
Stage 4: Implementing Proactive Security
Once the sites were fully cleaned, we proceeded to create a defensive perimeter to guarantee future security:
- Setting up a CMS-Level Firewall: Professional security plugins with built-in Web Application Firewall (WAF) were installed and configured.
- Brute Force Protection: Implementation of two-factor authentication for administrators, limiting login attempts, and blocking IP addresses.
- File Integrity Monitoring: Setting up a system that monitors any unauthorized changes to website files and instantly reports them, blocking a potential threat.
- Hosting Isolation: Account isolation was configured on the hosting for each site so that if one site were compromised, the virus could not spread to the others.
Stage 5: Relaunch and Monitoring
- Uploading Clean Sites: The cleaned and secured copies of the websites were uploaded back to the hosting.
- Functionality Testing: A full test of all functions, forms, galleries, and links was conducted.
- Post-Launch Monitoring: Over the following weeks, enhanced monitoring of traffic and file activity was established to ensure the absence of any hidden or recurring infection attempts.

 Input data
Input data  The result obtained
The result obtained